Overview
Our Vision
Velviyan Technologies aims to provide affordable digital transformation solutions and foster learning in the modern IT era
Our values
Innovation, integrity, collaboration, and excellence drive our commitment to delivering high-quality services.
VELVIYAN OFFERING NEWS ROOM
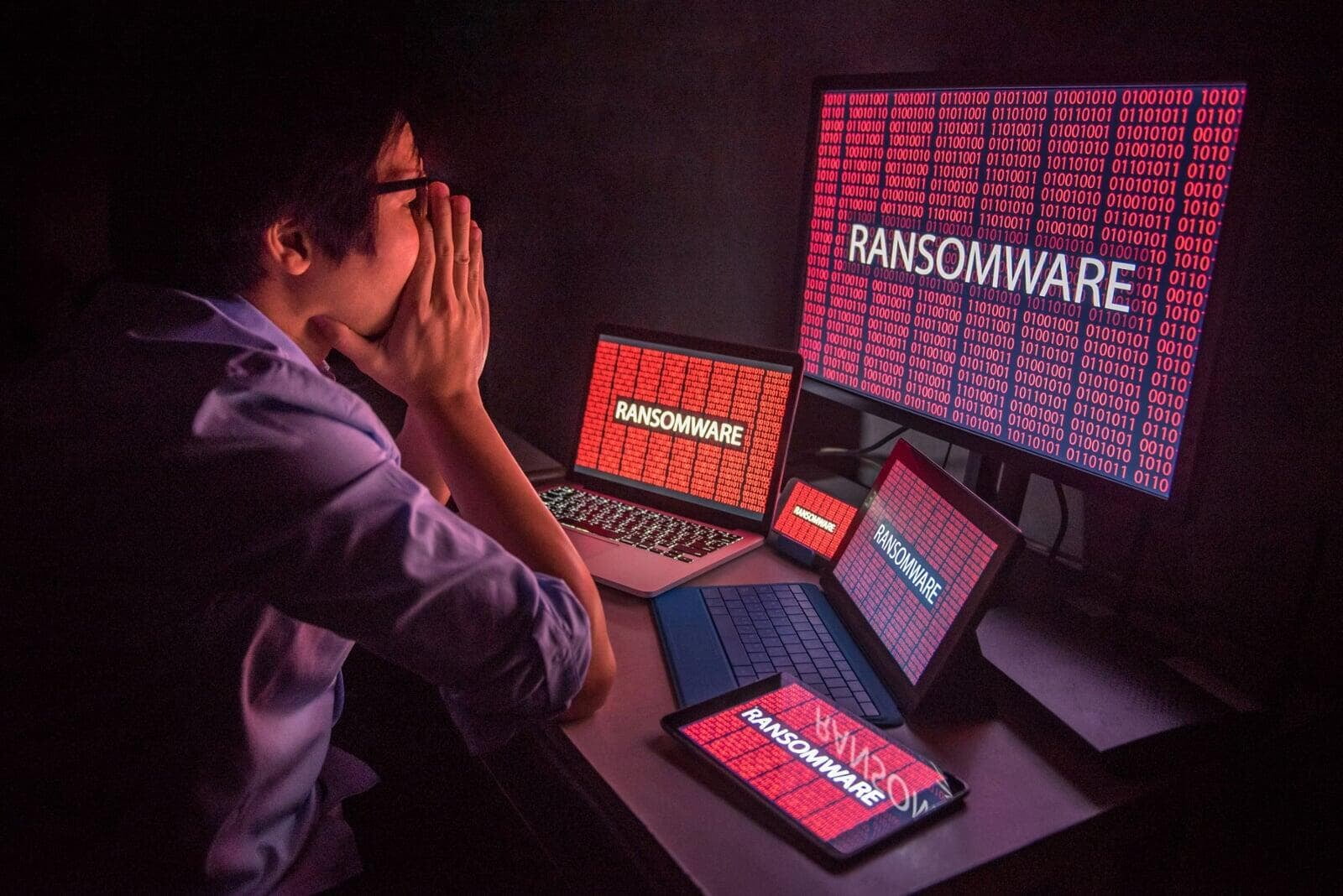
Ransomware Attacks on the Rise
Our framework ensures that each customer's data is logically separated from other customers data. Furthermore, we provide encryption at rest as well as in transit to protect our customers data. Data retention and backup happens in a secure manner.
Ransomware surges in Remote/Hybrid Environment
Our Product Security are secured by design, where every change and feature in our products goes through secure coding guidelines, code analyser tools, vulnerability scanners, and manual review processes. Our robust security framework based on OWASP standards, implemented in the application layer, provides functionalities to mitigate threats. Our employees think "security first" and we incorporate security into our entire software development process.
ISO 27001 & 22301 Certifications Made Simple:
Standards and regulations easy to understand and simple to implement. Whether you are just getting started or a skilled pro, our comprehensive software, tools, training, and resources enable you to execute any ISO project successfully. Now with AI.
Secure Printing
We’ve made security a cornerstone of our products from day one, so peace of mind is as simple as hitting ‘print’ from any device, printer, or app. Businesses spend billions on IT security and firewall protection every year, but some of the biggest (and simplest) security wins actually sit right under our nose at the printer.
It all begins with a fundamental understanding of a print job’s journey from submission to collection.
Secure Printing
We’ve made security a cornerstone of our products from day one, so peace of mind is as simple as hitting ‘print’ from any device, printer, or app. Businesses spend billions on IT security and firewall protection every year, but some of the biggest (and simplest) security wins actually sit right under our nose at the printer.
It all begins with a fundamental understanding of a print job’s journey from submission to collection.